You’re anchored securely in a tropical lagoon you used to dream about … then the “real world” drags you back. No matter how magical the anchorage, there comes the time when you have to dinghy ashore to seek out Wi-Fi and an Internet cafe so you can pay the bills, find parts, check in with family and friends and, if you are really courageous, read the news.
Today, voyagers enjoy a multitude of Internet benefits that make managing your real-world life much easier, but you best be aware of some new concerns. While voyaging, your online life will center around email. Almost every bill can be received via email. Many things that formerly were very difficult for voyagers to receive come via email. In addition, an email address is the necessary identifier you are using for everything from online banking to getting access to your online photos and calendar.
Like many of you, I have had a Gmail address since they were only available by invitation. Many years of my online life are referenced in gigabytes of email stored there — along with tons of sensitive information. The dilemma of online and cloud life is that it can be both tremendously useful and tremendously dangerous at the same time. All of that convenience comes with the danger that not only can you access your digital life anywhere, but so can the mythical 400-pound hacker lying in bed in New Jersey.
The 2FA two-step
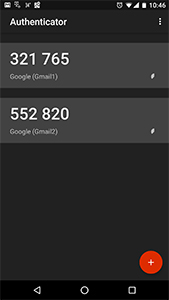
“Ah ha!” you say. “But, I have a password that is so strong even I can’t type it accurately, and I have turned on two-factor authentication!” The idea behind two-factor authentication (2FA) is great: You not only need something you know (your password) to log in, but you also need something you have (your smartphone) as a second step. A lot of us do this all the time — generate a code via an authenticator app or wait for an SMS text message to arrive, and then away we go looking up last year’s tax returns or grandma’s social security number, or transferring money between bank accounts. Google and other platforms highly recommend that we all use 2FA wherever possible, and so do I.
Now back to the tropical lagoon where your boat sits at anchor. You zip ashore in the dink, find a cool Internet cafe with Wi-Fi, fire up the computer, maybe connect via a virtual private network (VPN) for extra security, then you try to log in to Gmail. The GMaster recognizes you are not logging in from Podunk, Iowa, then promptly prompts you to use your authenticator app. But wait, you lost your phone four weeks ago when you dropped it in the harbor as you were hauling the anchor in the Galapagos. Okay, that means no SMS messages either. How about those backup codes you printed out and stored safely someplace on the boat? The question is where did I put those dang (substitute appropriate language here) things!
Luckily, your wife, smart person she is, remembers exactly where those codes are — in the safe deposit box in Podunk. Great, now what? You’ve got backup email addresses and phone numbers set up, right? Well, one is grandma’s and she never checks her email and has forgotten her password. You discover this by making an expensive call home, waking her in the middle of the night, and then waiting 10 minutes for her to find and put in her hearing aid. The other backup is your wife’s phone number and she cancelled that when you set sail. You get the picture.
 |
|
An example of two-factor authentication. |
|
John Kettlewell |
You are a product, not a customer
Now comes the fun part. Remember all that great free stuff Google gives you? It isn’t free. In exchange for letting you enjoy the Internet good life, Google mines that life for everything you are worth. Many of us put up with this in exchange for free, free, free! Since all of this free stuff costs billions of dollars to create, maintain and secure, Google has cut expensive support to the bone. Good luck trying to reach a human being to explain your problems to: “I’m on a sailboat in the South Pacific in this beautiful tropical lagoon sipping pina coladas in a waterfront bar and I need help getting into Gmail.” Luckily, there is no way to reach anyone to tell your embarrassing sob story to. Instead, start filling out online forms that ask you for all those things we just identified as being unavailable to you: your phone number (sunk), your alternate email address (grandma can’t access), your wife’s phone number (cancelled), your codes (in the safety deposit box), etc.
Sound far-fetched? Do some Googling around and you will find many horror stories, including some from people who were never able to regain access to their Google accounts. In my own experience, you can easily get locked out of your Google account when traveling overseas for even short periods of time. I flew to Australia and was staying in a nice hotel with Internet access, but Google, in its wisdom, determined I was logging in from an unusual location and blocked me. At the time I was using SMS for 2FA and my phone number wouldn’t work in Australia. My backup email and phone were my wife’s and I couldn’t reach her easily because of the time (and day) difference, my printed codes were safely stored at home, and the phone and service I purchased locally was requiring me to click on some activation link they had sent to my Gmail address that I couldn’t access! I eventually sorted out the problem, but was never able to get into my work email account because their security settings were such that all access was blocked from foreign locations.
There is no (metaphor alert!) Holy Grail full of magic bullets to solve the security vs. availability paradox, but there are some options that can help. First, it is important to turn on and use 2FA on whatever important accounts you have: email, banking, investments, taxes, Amazon, PayPal, etc. Personally, I’m not so worried about many other logins (e.g., forums, clubs, memberships). Social media accounts can be very dangerous, especially if you’ve used that convenient option to log in to other accounts using your Facebook or other profile. Just the life details that can be mined from social media can make you very vulnerable to online attacks. For example, your Facebook account may very well contain the answers to some of those annoying security questions you have answered, such as the name of your first pet or your mother’s maiden name.
Password managers
Hopefully you agree that strong passwords and 2FA are important. Use a password manager, too, so you don’t have to remember those strong passwords and also so you can use unique ones on every site. Those steps are just basic Internet hygiene.
There are ways to mitigate the Gmail problem. First, consider using an alternate email address that you control, not one that might be out of your control (like grandma’s). Keep in mind the possibility that it might also be very hard to get into this alternate email address due to the same factors that are blocking your access to the main account. For example, your alternate address for Gmail should not be another similarly secured Gmail account! You may want to consider using a relatively insecure email address with no 2FA turned on for that alternate address. Just be careful to never use that insecure email address for anything important. Make sure you keep the password to the alternate somewhere you will always have with you, or make it one you can never forget. Have all messages from the insecure account forwarded to your secure account too, just in case someone is trying to reach you that way and to alert you if for some reason the insecure account is hacked.
The insecure account can be very useful for general communication purposes if you have the discipline to never use it for anything that would be of interest to the 400-pound hacker. Most of us aren’t that careful and don’t have the spy’s ability to maintain two online personalities. At home I have an old phone plugged in and logged in to an old email address I stopped using years ago. I am frequently surprised, not in a good way, at the important emails that show up from the old address. For example, one utility company still sends my bills to that address in addition to my current email address. I have tried to get the old address removed numerous times and it never works. Which brings up an important point: Any email address you use must be secured to a level appropriate to what vulnerable information might be collected there. Consider closing old accounts that you no longer use as they create chinks in your online armor.
 |
|
With kids using the Internet aboard, the possibilities for inadvertently downloading malware increase. |
|
John Kettlewell |
Think really carefully about backup phone numbers. For example, in the past I have caught myself using a work number that unfortunately couldn’t receive text messages — whoops! Similarly, don’t forget to check the numbers securing your account periodically. People move, change numbers, die and then you’re sunk. Another problem that should be obvious is the difficulty in reaching someone back home in a different time zone, who is possibly not able to access the phone or email you have provided. Many cellphones are unable to receive calls from areas outside the home country, or sometimes calls from certain countries are blocked. Other times you can’t get calls back from someone using only a mobile phone because they don’t have the ability to call out of the country. Anyone who has voyaged knows the situation well. I tell loved ones and friends, “Don’t worry unless you hear from me.”
The code
Google’s backup codes could be a good answer, and storing them in printed form somewhere on board is probably a good idea if location is reasonably secure and you will never forget it. I wouldn’t put them anywhere near anything with my email address on it just in case I happen to be pickpocketed or the boat is ransacked. Here’s what Google says about backup code use (also available at support.google.com/accounts/answer/1187538?hl=en):
“If you lose your phones or otherwise can’t receive codes via SMS, voice call or Google Authenticator, you can use backup codes to sign in … You can also use these codes to sign in if you don’t have your Security Key.
“The codes come in sets of 10, and you can generate a new set at any point, automatically making the old set inactive. In addition, after you’ve used a backup code to sign in, it will become inactive.
“We recommend you store your codes wherever you keep your other valuable items. Like the codes on your phone, backup codes are only valuable to someone if they manage to also steal your password.”
Despite what Google recommends, I don’t think backup codes should be stored where “you keep your other valuable items.” Imagine what life would be like if your boat was ransacked. You would need to quickly go online to change passwords, secure bank accounts, possibly transfer money to replenish stolen funds, etc. If your backup codes get stolen, your life might become even more difficult. Instead, consider the “plain sight” method of security. There are many great ideas out there such as storing codes on a card in the middle of a deck of cards. With this type of trick, you have to be careful not to accidentally give away the pack of cards, or forget where you put it. I bought a boat once that had foreign currency stored behind some ceiling panels. I found it when I was re-bedding some deck fittings. Obviously, the previous owner had forgotten about the hiding place — don’t let that happen to your codes! For some things like this, I put them in a location that I know I periodically access, reminding me at intervals where the secrets are hidden. Your secret location is worthless if it is so obscure that even you forget about it, just like a password that is so strong even you can’t type it in accurately!
One size fits nobody
Like most things in life, email security is not a one-size-fits-all situation. You need to explore your own security vulnerabilities to find a solution that works for you, but you do need to think carefully about these things before you leave the real world behind with its ubiquitous connectivity that can be both convenient and a trap.
John Kettlewell is a constituent engagement director at Saratoga PLAN, a land conservancy. When not protecting open land spaces, he sails open waters aboard his 38-foot motorsailer, Minke. For about 40 years he’s been sailing between Labrador and Colombia, and he’s the author of The Intracoastal Waterway Chartbook.